In today’s digital age, the topics of security and compliance are of utmost importance for individuals and organizations alike. While both aim to protect sensitive data and ensure the smooth functioning of operations, they have distinct roles and approaches. This article delves into the similarities and differences between security and compliance, shedding light on their significance and highlighting their respective focuses.
Table of Contents
Understanding Security
IT security is a multifaceted and continually evolving discipline that demands ongoing diligence and attentiveness. To guarantee the safety and security of your IT systems and data, it is vital to establish resilient security measures, remain updated with the latest threats and vulnerabilities, and provide comprehensive training to employees on best practices.
What is Security?
IT security, also known as information security, pertains to the act of safeguarding computer systems, networks, and data from unauthorized access, theft, damage, or disruption. It holds immense importance for organizations across various sizes and industries, as they heavily rely on technology to store, process, and transmit sensitive information. The field of IT cybersecurity encompasses a range of technologies, processes, and policies that are employed to shield digital assets and ensure the confidentiality, integrity, and availability of sensitive data.
The domain of IT security employs diverse methods and technologies to fortify systems and data against cyber threats. These threats include malware, ransomware, phishing attacks, social engineering, and other forms of cyberattacks. Cybersecurity professionals utilize an array of tools and techniques to identify vulnerabilities and risks within IT systems, subsequently implementing controls and procedures to mitigate these risks.
Maintaining robust IT security is paramount for any organization seeking to safeguard its digital assets and sensitive information. Given the rising sophistication and frequency of cyber threats, organizations must proactively fortify their systems and data. By implementing comprehensive IT cybersecurity measures, organizations can effectively shield their digital assets and sensitive information, diminish the risk of cyberattacks, and uphold the trust of their customers and stakeholders.
Types of Security Threats
Security threats come in various forms, each with its own potential impact on computer systems, networks, and data. Following are some common types of security threats:
- Malware: Malware, short for malicious software, is a broad category that includes viruses, worms, Trojans, ransomware, spyware, and adware. Malware is designed to infiltrate systems, disrupt operations, steal data, or gain unauthorized access. It can be delivered through infected emails, malicious websites, or compromised software.
- Phishing Attacks: Phishing attacks involve deceptive techniques to trick individuals into revealing sensitive information such as usernames, passwords, or financial details. Attackers typically masquerade as trustworthy entities, often through email or fake websites, aiming to manipulate recipients into providing their confidential data.
- Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks: DoS and DDoS attacks aim to overwhelm a system or network, rendering it inaccessible to legitimate users. Attackers flood the target with an overwhelming volume of traffic or requests, causing a disruption in service and potentially leading to financial losses or reputational damage.
- Social Engineering: Social engineering involves manipulating individuals to divulge confidential information or perform certain actions that may compromise security. Attackers exploit human vulnerabilities, using techniques such as impersonation, pretexting, or baiting to deceive and manipulate people into providing sensitive data or granting unauthorized access.
- Insider Threats: Insider threats pertain to the security risks that arise from individuals within an organization who possess authorized access to systems and data. These threats can be intentional, such as when employees misuse their privileges for personal gain, or unintentional, such as when employees inadvertently disclose sensitive information or fall victim to phishing attacks.
- Password Attacks: Password attacks involve unauthorized attempts to obtain passwords to gain access to systems or accounts. Common techniques include brute-force attacks, where attackers systematically try various password combinations, and dictionary attacks, where commonly used passwords are attempted.
- Man-in-the-Middle (MitM) Attacks: In MitM attacks, an attacker intercepts and alters the communication between two parties without their knowledge. This allows the attacker to eavesdrop, steal data, or manipulate the information being exchanged.
- SQL Injection: SQL injection attacks target web applications that interact with databases. Attackers exploit vulnerabilities in the application’s code to inject malicious SQL statements, potentially gaining unauthorized access to the database or manipulating its contents.
- Zero-day Exploits: Zero-day exploits target vulnerabilities in software that is unknown to the software vendor. Attackers leverage these vulnerabilities before a patch or update is available, putting systems at risk.
- Physical Threats: Physical threats involve unauthorized access to computer systems, networks, or data through direct physical means. This can include theft of hardware, unauthorized access to server rooms, or tampering with devices.
Understanding Compliance
Compliance is an integral aspect of the overall security stance of an organization. Its purpose is to ensure that the organization operates ethically and legally while meeting the industry and regulatory requirements it is subject to. Compliance encompasses a wide array of areas, including data privacy, information security, financial reporting, and environmental regulations.
What is Compliance?
Compliance entails adhering to laws, regulations, and standards that govern the handling and processing of data. Its objective is to ensure that an organization follows the rules and regulations set forth by regulatory bodies relevant to its industry and the type of data being managed. These regulatory bodies can include HIPAA, PCI-DSS, GDPR, SOC, and others. In the context of information security, compliance signifies that an organization has implemented and maintained adequate security controls and procedures to safeguard sensitive data and fulfill regulatory obligations.
Compliance is not merely an option but a legal obligation that organizations must fulfill to avoid fines, legal sanctions, and damage to their reputation. Compliance requirements are typically established by governing bodies, such as government agencies or industry associations. Non-compliance can result in severe consequences, including financial penalties and the loss of business opportunities. While certain compliance frameworks are mandatory, others serve as guidelines to align with industry best practices.
For example, Service Organization Control Type 2 (SOC 2) is a framework that businesses may choose to adopt as guidance for securely handling data. On the other hand, the Health Insurance Portability and Accountability Act (HIPAA) is a compliance framework that healthcare companies are obligated to comply with.
Types of Compliance Regulations
Compliance regulations vary across industries and jurisdictions, and organizations must navigate a complex landscape to ensure they meet the specific requirements that apply to them. Here are some common types of compliance regulations:
- Data Protection and Privacy Regulations:
- General Data Protection Regulation (GDPR): Applicable to organizations operating in the European Union (EU) or handling EU citizen data, GDPR sets rules for the collection, processing, and protection of personal data.
- California Consumer Privacy Act (CCPA): Pertains to businesses that collect and process personal information of California residents, providing consumers with certain rights regarding their data.
- Financial Regulations:
- Sarbanes-Oxley Act (SOX): Applies to publicly traded companies in the United States, requiring them to establish and maintain internal controls to ensure accurate financial reporting and prevent fraud.
- Payment Card Industry Data Security Standard (PCI DSS): Imposed by major credit card companies, PCI DSS mandates security controls for organizations handling credit card transactions.
- Healthcare Regulations:
- Health Insurance Portability and Accountability Act (HIPAA): Applicable to healthcare providers, health plans, and clearinghouses in the United States, HIPAA sets standards for protecting patients’ electronic health information through the use of a HIPAA form and other tools.
- Health Information Technology for Economic and Clinical Health Act (HITECH): Expands upon HIPAA by emphasizing the secure handling of electronic health records and implementing breach notification requirements.
- Industry-Specific Regulations:
- Basel III: Banking regulations aimed at strengthening the resilience of the banking sector and improving risk management practices.
- Federal Energy Regulatory Commission (FERC) Standards: Applies to the energy sector, setting requirements for cybersecurity measures to protect critical infrastructure.
- Anti-Money Laundering (AML) Regulations:
- Financial Action Task Force (FATF) Recommendations: A global standard for combating money laundering, terrorist financing, and other financial crimes.
Differences between Security and Compliance
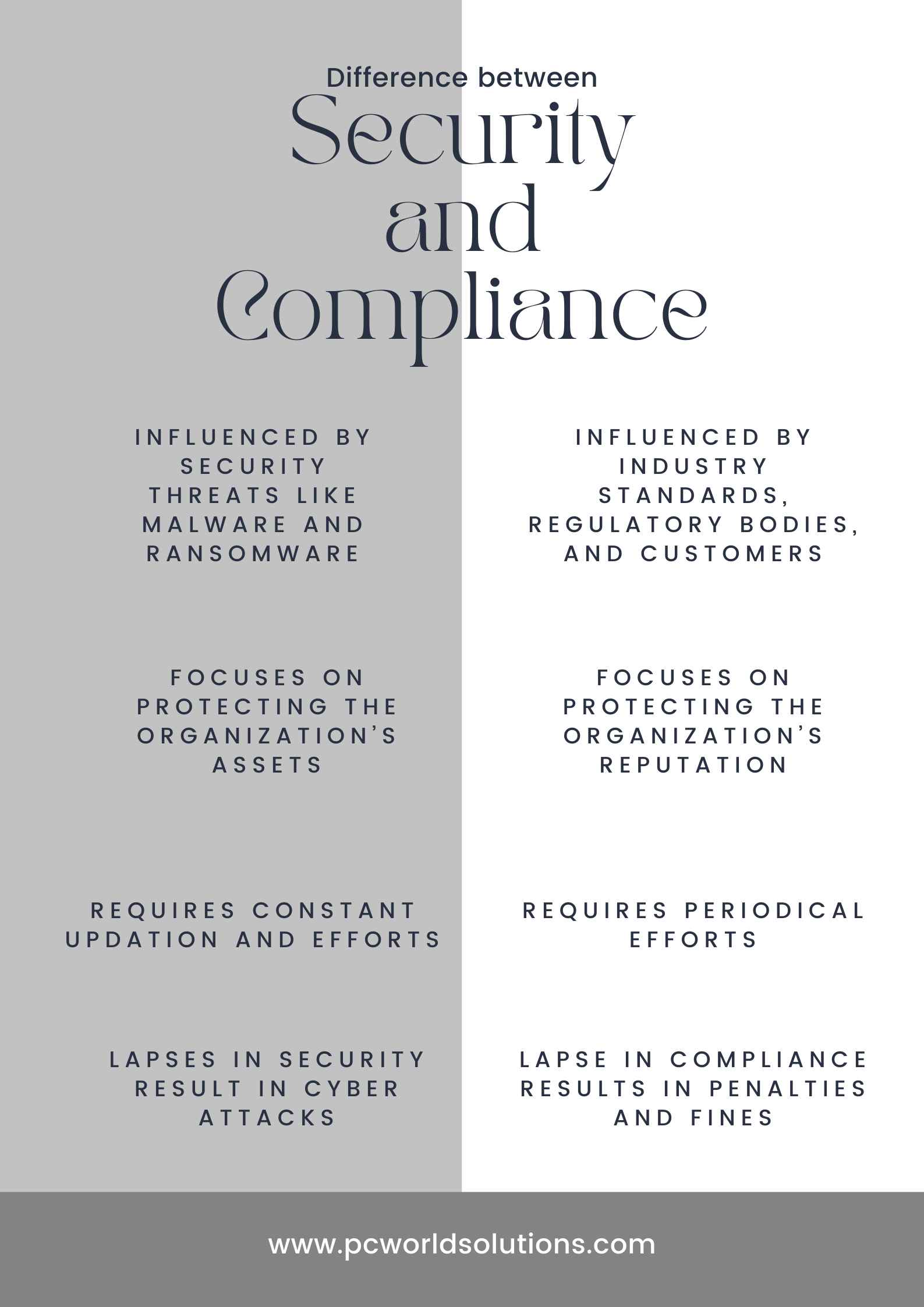
Focus
The primary difference between security and compliance lies in their focus. Security concentrates on protecting assets, data, and systems from various threats, both external and internal. It encompasses measures such as firewalls, encryption, access controls, and incident response planning. Compliance, on the other hand, centers around meeting legal, regulatory, and industry-specific requirements and standards. It ensures that organizations operate within the boundaries defined by applicable laws and regulations.
Goal
The ultimate goal of security is to maintain the confidentiality, integrity, and availability of assets and data. It aims to prevent unauthorized access, data breaches, and system disruptions, ensuring that information remains secure. Compliance, on the other hand, strives to achieve adherence to specific laws, regulations, or industry standards. Its objective is to avoid legal consequences, penalties, and reputational damage resulting from non-compliance.
Approach
Security and compliance employ different approaches to achieve their objectives. Security focuses on implementing technical and procedural controls to safeguard assets. This includes deploying firewalls, intrusion detection systems, encryption, multi-factor authentication, and security awareness training. Compliance, however, involves establishing policies, procedures, and governance structures to ensure adherence to regulations and standards. It requires documentation, audits, and regular assessments to validate compliance.
Stakeholders
Security efforts involve various stakeholders, including IT teams, cybersecurity professionals, system administrators, and end-users. Their collective responsibility is to implement security controls and adhere to security policies. Compliance, on the other hand, extends beyond the IT department and involves legal and regulatory experts, executives, auditors, and compliance officers. These stakeholders work together to understand, interpret, and implement applicable regulations and standards.
Relationship between Security and Compliance
Security and compliance are interconnected concepts that hold significant importance in safeguarding an organization’s information technology assets. As mentioned earlier, compliance forms an integral component of the comprehensive IT security posture. Consequently, these two aspects are closely intertwined and frequently collaborate to accomplish shared objectives.
Protection of Assets
Both security and compliance share the common objective of safeguarding assets. Security measures are designed to protect systems, networks, applications, and data from unauthorized access, breaches, or attacks. Compliance, on the other hand, aims to ensure adherence to relevant laws, regulations, and industry standards, which indirectly contributes to the protection of assets.
Risk Management
Both security and compliance efforts are driven by risk management principles. Security practices aim to identify potential risks and vulnerabilities, implementing controls and countermeasures to mitigate or minimize them. Compliance focuses on identifying regulatory and legal risks, aiming to meet the requirements and avoid penalties or legal consequences.
Continuous Improvement
Both security and compliance are ongoing processes that require continuous improvement. In the realm of security, new threats and vulnerabilities emerge regularly, necessitating constant monitoring and updates to security measures. Similarly, compliance regulations evolve, requiring organizations to adapt and maintain compliance with changing standards.
Importance of Policies and Procedures
Both security and compliance rely heavily on the development and implementation of robust policies and procedures. Security policies define the rules and guidelines for protecting assets, while compliance policies outline the organization’s commitment to adhering to specific regulations and standards. These policies form the basis for establishing controls and ensuring consistent practices throughout an organization.
Conclusion
While security and compliance share some similarities in their quest to protect assets and manage risks, they have distinct focuses and approaches. Security concentrates on safeguarding assets from threats and breaches, aiming to maintain confidentiality, integrity, and availability. Compliance, on the other hand, revolves around meeting legal and regulatory requirements, ensuring adherence to specific standards. Both security and compliance are essential components of a comprehensive risk management strategy, and organizations must address both aspects to achieve a robust and compliant operational environment. By understanding the similarities and differences between security and compliance, organizations can develop a holistic approach that protects their assets while meeting regulatory obligations.

